
Govern KMS Keys with Certainty, Not Spreadsheets.
Auto-rotation is not governance. Scope to PII in prod, see blast radius, and export proof on demand.
Request a Demo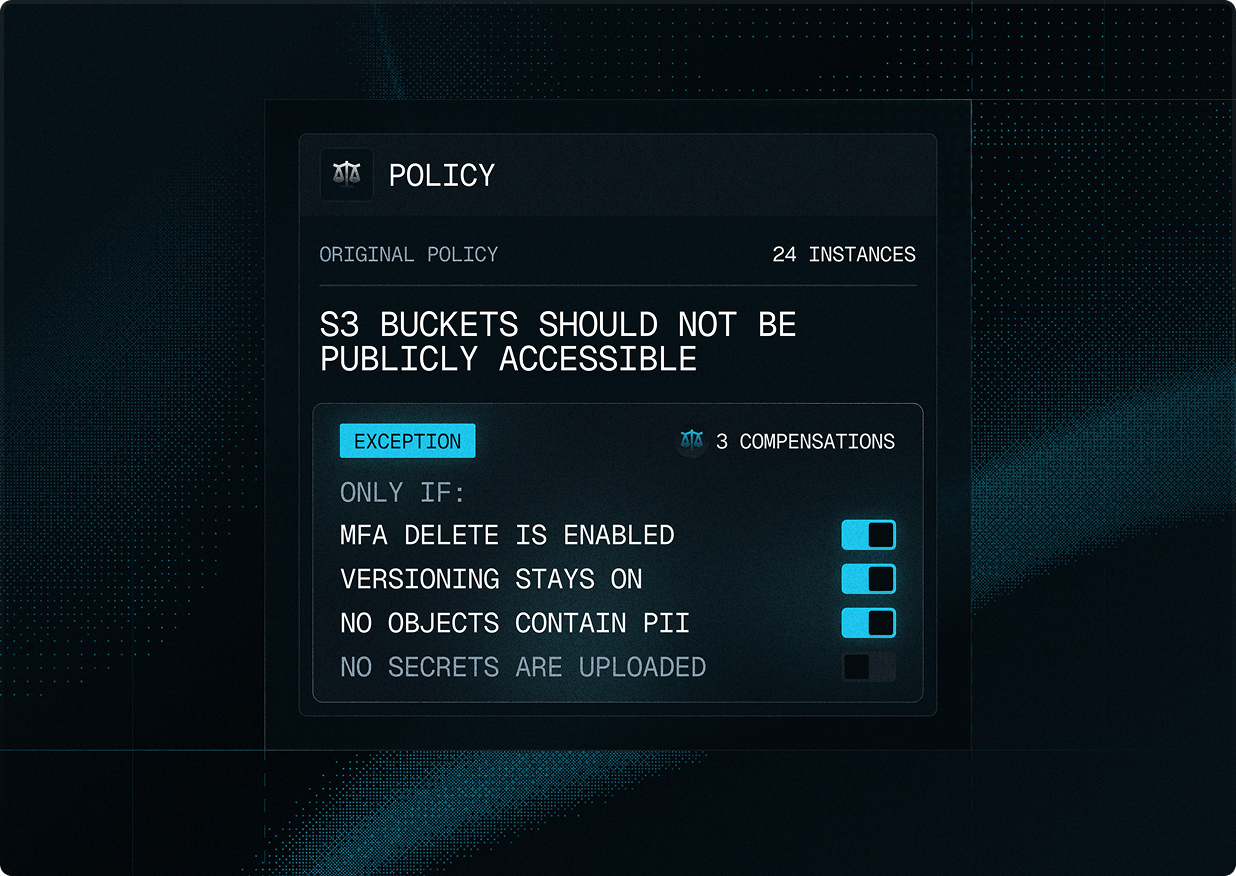
“imPAC's detailed reports and alerts help us make informed decisions quickly. It's a game-changer for our security”
-James Lange, CISO, Odeao Labs
See Hidden Connections. Understand True Risk.
When a misconfigured S3 bucket triggers an alert, Asset Chains show you the complete context:
- Is it connected to sensitive data?
- What IAM roles can access it?
- Which encryption keys protect it?
This context illustrates the difference between false positives and real threats.
See it in Action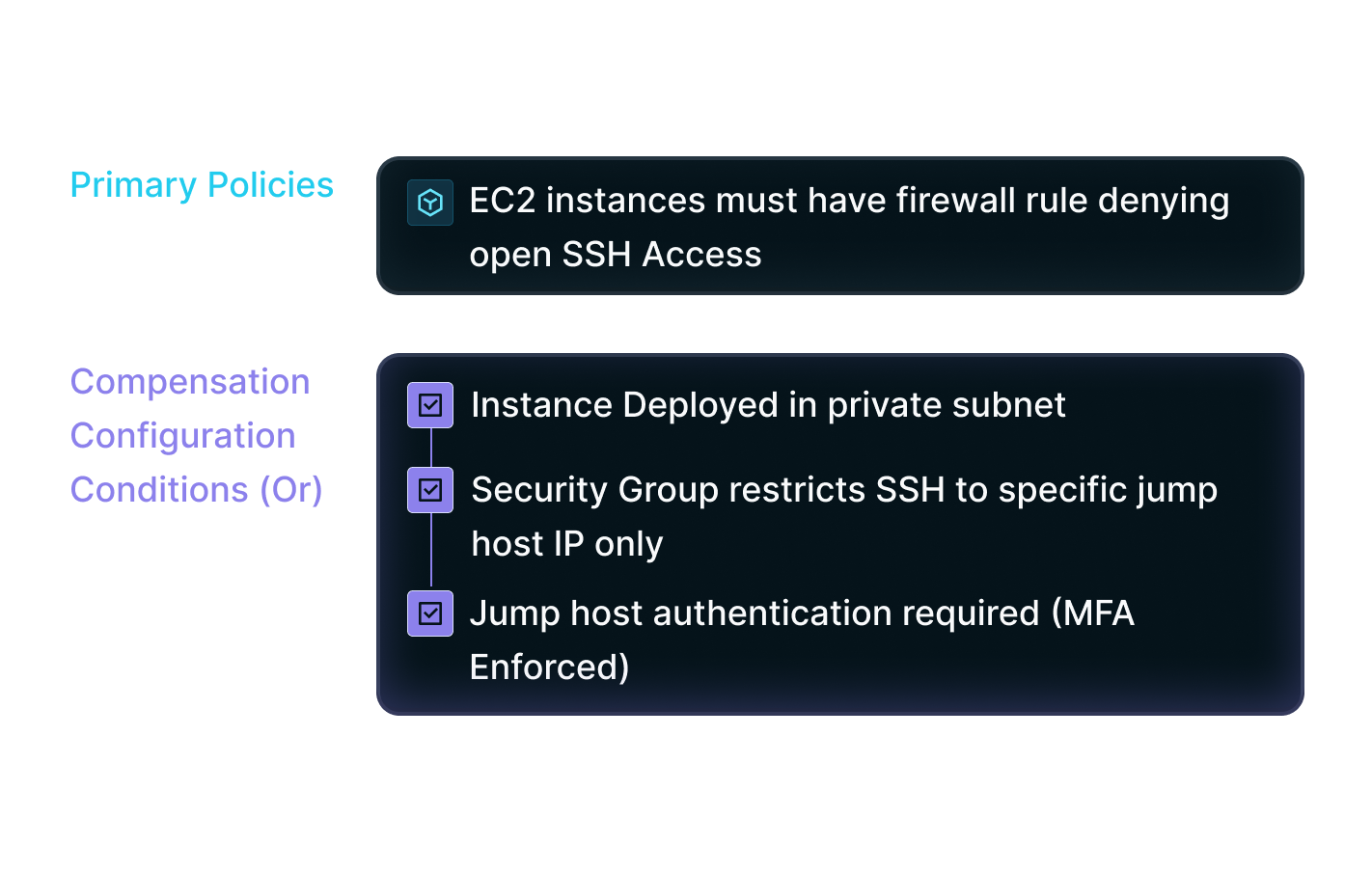
How It Works
When a misconfigured S3 bucket triggers an alert, Asset Chains show you the complete context:
Automatically discover and group related resources
Track configurations across all connected assets
Map complete relationship chains (S3 → IAM → keys)
Monitor changes across asset relationships
Business Impact
Enable Holistic Security
Apply consistent controls across all connected cloud assets
Cut Through the Noise
Reduce alert fatigue with accurate info on asset context and relationships
Scale Policy Management
Automatically enforce policies as cloud environments grow
Automate Governance
Replace manual checks with automated, chain-wide policy enforcement
Ready to Extend Your Data Protection from Users to Cloud Infrastructure?
Request a Personalized Demo and see how imPAC secures your sensitive data across its entire lifecycle.